IT that runs itself. With engineers on standby.
Corax monitors, diagnoses, and fixes your infrastructure around the clock without human intervention. Senior engineers are available if you need them. Most of the time, you won't.
Fully autonomous. Engineers on call, not on the clock.
Server errors
detected & healed
Security threats
neutralized in seconds
Network outages
predicted & prevented
Compliance gaps
caught & remediated
Built by senior infrastructure engineers with 60+ years of combined enterprise experience
Proof, not promises
Every test runs against the production Neural Engine. Every result is public.
From zero to fully managed in minutes
Deploy once. Corax handles everything from there.
Deploy
Install the Corax agent on any network with a single command. Windows, macOS, and Linux. No firewall changes required.
Discover
Agents scan and map every device, service, and dependency on your network automatically. Full topology in minutes.
Monitor & Protect
Continuous monitoring, security scanning, and compliance checks run around the clock across your entire infrastructure.
Act
Corax fixes issues autonomously, optimizes infrastructure, generates reports, and escalates only when human judgment is needed.
Every process is a workflow. Every workflow improves itself.
Most platforms hard-code their logic. When something changes, a human has to rewrite the rules. Corax runs every operation through intelligent, observable workflows that the AI continuously analyzes, questions, and enhances to meet the specific needs of your business.
Everything is visible
Monitoring, incident triage, healing, security response, ticket routing, report generation, agent communication, credential access. Every process runs as an observable workflow with a full execution trace, not buried in code that only engineers can read.
The AI questions everything
Corax continuously asks itself: What should we be doing that we are not? Are we delivering on what we promised? What patterns keep recurring that we should automate? What would make this better for the customer? These questions are generated dynamically based on what the system is currently analyzing.
Workflows evolve on their own
When the AI discovers a gap, a repeated failure pattern, or a better approach, it modifies the workflow. New automation gets created, existing processes get refined, and the system adapts to your environment. Fully autonomous, or with approval gates if you want sign-off first.
Oracle Incident Triage
15 nodes · 16 edges · v6 · ORACLE
Always Logged
Every incident creates a ticket before any action. Full audit trail, no exceptions.
Human in the Loop
Optional approval gates let customers control trust levels. Fully autonomous or human-approved.
Verified Healing
Auto-heals are tested and confirmed. If verification fails, Corax escalates automatically.
Traditional platforms do what they were programmed to do. Corax figures out what needs to be done, builds the process, runs it, measures the result, and improves it. Continuously. For every customer. Across every domain.
The brain behind every decision
Corax combines its own trained ML models with LLM reasoning to build an AI engine that no single technology could deliver alone. It learns what normal looks like, detects anomalies the moment they appear, and makes autonomous decisions with full transparency.
Adaptive Baselines
The Neural Engine builds rolling statistical baselines for every metric on every monitor. Response times, error rates, CPU loads, connection counts. It knows what “Tuesday at 3 PM” normally looks like for each system, so it can spot deviations that fixed thresholds would miss entirely.
Anomaly Detection
Using statistical analysis against learned baselines, Corax detects performance degradation, traffic anomalies, and resource pressure before they escalate into outages. No manual threshold tuning required. The engine adapts as your infrastructure evolves.
Incident Correlation
When multiple systems fail within the same time window, the Neural Engine automatically correlates them. It identifies the root cause incident and marks downstream symptoms, so your team sees one problem to solve instead of a dozen disconnected alerts.
Full Decision Transparency
Every decision the Neural Engine makes is logged with its reasoning, confidence score, and the data that informed it. You can review why Corax chose to heal, escalate, or wait on any incident. No black boxes.
Five AI agents deliberate before Corax touches anything
Autonomous doesn't mean reckless. Before any destructive action, Corax convenes a quorum of five specialized AI agents. Each analyzes the proposed action from a different angle: infrastructure health, network topology, policy compliance, blast radius impact, and historical outcomes. They vote independently, dissenting opinions are logged, and a weighted consensus determines whether Corax proceeds, defers, or escalates to a human.
Decision Rules
- Every vote persisted with full reasoning and confidence scores
- Dissenting opinions logged even when overruled by consensus
- Policy agent has weighted veto power for compliance mandates
- Integrates blast radius, knowledge graph, and incident history
- Dashboard audit trail of every quorum session and outcome
Network Peer Verification
Before the AI Quorum even convenes, local agents on the same network cross-verify reachability. If peers can still reach a device, Corax knows it's a path problem, not a real outage, and skips the false alarm entirely.
Sentinel detected the primary PostgreSQL server stopped responding. Healing engine proposes a service restart.
CPU at 4%, memory stable. No active transactions. Safe to restart the service.
No upstream routing changes. Replicas healthy. Clients can failover during restart.
Break-glass invoked: service is down, maintenance window restriction waived for active outage.
12 dependent services affected. Read replicas absorbing queries. Restart impact: ~15 seconds.
Same restart succeeded 3 times in 90 days. Average downtime: 8 seconds. No regressions.
AI that learns your network
Most AI platforms send your data to a generic LLM and hope for the best. Corax runs 8 purpose-built TensorFlow neural networks that train on your specific infrastructure from day one. They learn your network topology, your traffic patterns, your peak hours, your time-of-day baselines. Combined with LLM reasoning for complex analysis, the result is an AI that understands what “normal” looks like for your environment and catches the anomalies that generic tools miss entirely.
Trained on real IT data. Refined on yours.
We designed and trained all 8 Cortex models in-house using TensorFlow and Keras on real-world IT operations data. When you onboard, these models begin training on your specific environment: your device topology, your traffic baselines, your error patterns, your business hours. A 2 AM CPU spike on your backup server is normal. The same spike on your production database at peak hours is not. Corax learns the difference. LLM reasoning via providers like Anthropic and Azure OpenAI handles complex analysis, while our trained models handle the fast, continuous pattern recognition underneath.
21ms
Ticket routing inference
35ms
Vulnerability scoring
43ms
Topology analysis
46ms
Compliance auditing
ML pre-screening eliminates 70% of unnecessary LLM calls
Sentinel
~1.2sLSTM Autoencoder
Anomaly detection across telemetry sequences. Learns normal infrastructure patterns and flags deviations before they become outages.
Atlas
~43msGraph Attention Network
Topology intelligence. Analyzes node criticality, link health, failure risk, and blast radius across your entire infrastructure graph.
Garrison
~414msBiLSTM + Attention
Threat classification across 15 threat types and 7 kill chain stages. Scores containment priority and lateral movement risk.
Dispatch
~21msMulti-head Classifier
Ticket routing. Predicts priority, category, team assignment, resolution time estimate, and auto-resolution likelihood.
Ledger
~1.2sCost LSTM Autoencoder
Cost anomaly detection and 30-day spend forecasting. Flags budget overruns and identifies billing anomalies before they compound.
Auditor
~46msAttention Classifier
Compliance scoring across 6 frameworks. Evaluates control configurations and prioritizes remediation by violation severity.
Compass
~422msMetric LSTM Forecaster
30-day capacity forecasting, health scoring, and trend analysis. Predicts when you'll hit resource limits before you get there.
Vanguard
~35msAttention Risk Scorer
Vulnerability ranking by exploit likelihood and remediation priority. Cuts through scan noise to surface real threats.
Your infrastructure, your rules
For organizations with strict data residency, compliance, or sovereignty requirements, Corax deploys our trained ML models directly onto your infrastructure. The LLM reasoning layer integrates with your approved provider: Azure OpenAI, AWS Bedrock, Google Vertex AI, or any OpenAI-compatible endpoint. Your data never leaves your environment. Your security team stays in control.
On-prem ML deployment
Cortex models run inside your network
Bring your own LLM
Azure OpenAI, AWS Bedrock, Vertex AI
Data never leaves
Full data residency compliance
Audit-ready
SOC 2, HIPAA, FedRAMP compatible
Other AI tools forget.
Corax remembers.
Every AI tool on the market has the same problem: close the session, open it again, and it has no idea who you are, what it did yesterday, or why your firewall is configured that way. Some try to fix this with static memory files that get dumped into every prompt, burning through tokens just to reconstruct context that should already be there.
Corax takes a fundamentally different approach. Every incident resolved, every person contacted, every device configured, every lesson learned gets woven into a living knowledge graph with relational mappings across your entire business. People, systems, policies, skills, history. All connected. All queryable. All growing.
People Intelligence
Every contact, their role, their skill level, their communication preferences. Corax adjusts technical depth per person automatically. Sarah gets the executive summary. Mike gets the packet capture.
Business Context
Maintenance windows, revenue-critical services, seasonal patterns. When the payment gateway goes down at 2 AM on Black Friday, Corax already knows this is a five alarm fire, not routine maintenance.
Learned Skills
Every successful fix becomes a reusable skill. Skills promote from device-specific to org-wide to platform-wide as they prove reliable. Your lessons learned become everyone's lessons learned.
Relational Memory
Not a flat file. A graph. When Server 7 goes down, Corax instantly knows the blast radius: which services depend on it, who to notify, what worked last time, and which maintenance window to respect.
Enterprise security, built in
Every layer of Corax is designed for environments where security and compliance are non-negotiable.
AI never sees your secrets
Corax uses a cryptographic credential enclave to architecturally isolate your API keys, tokens, and passwords from the AI engine. The LLM orchestrates actions using opaque references. Real credentials are injected only at the API call boundary, inside a sealed execution context that auto-zeroes memory after use.
→ sees: [CREDENTIAL:cref_a8f3...]
→ resolves opaque ref → real value
→ Authorization: Bearer ••••••••
→ leak scanner: CLEAN ✓ memory zeroed
AES-256-GCM at Rest
All stored data encrypted with AES-256-GCM. Database connections require TLS.
TLS 1.3 in Transit
All agent, API, and WebSocket connections encrypted with TLS 1.3. No plaintext, ever.
HMAC-SHA256 Signed Messages
Every Redis pub/sub message cryptographically signed to prevent tampering or replay.
Approval Gates & Audit Trail
Destructive actions require human approval. Every action logged with full reasoning chain.
Zero Data Training
Your data is never used to train AI models. Anthropic zero-retention API policy enforced.
SOC 2 / HIPAA / PCI-DSS / CIS
Built-in compliance scanning and reporting for major regulatory frameworks.
HIPAA Ready with BYOC
Business and Enterprise plans support Bring Your Own Claude for full data residency control.
SOC 2 Type II Controls
SOC 2 Type II controls in place across infrastructure, access management, and operations. Formal audit in progress.
14 AI specialists. Fully autonomous. Zero hand holding.
Monitoring, triage, remediation, security, compliance, and operations. All running without human intervention. Engineers on standby if you want them.
24/7 Autonomous Monitoring
Continuous health checks across every protocol. HTTP, PING, TCP, DNS, certificates, SNMP, and custom scripts. Sub-second detection of downtime, errors, and performance degradation.
AI Diagnosis & Healing
When something breaks, Corax reads your code, analyzes logs, and pinpoints the root cause. Then it writes the fix, deploys it, and verifies recovery. Average resolution under 3 minutes.
Network Discovery & Topology
Deploy agents on any network and Corax maps every device, service, and dependency automatically. Live topology views show exactly what is running and how it all connects.
Security & Compliance
Continuous vulnerability scanning, configuration audits, and compliance checks against industry frameworks. Corax identifies risks and remediates them before they become incidents.
Client Portal & Reporting
Give every client their own portal with real-time status, incident history, and SLA metrics. Automated quarterly business reviews and operations reports, ready to present.
Reports & Business Intelligence
Automated weekly and monthly operations reports, quarterly business reviews, cost optimization analysis, and capacity forecasting. Data driven decisions without the analyst.
Meraki has an AI assistant.
 has autonomy.
has autonomy.
Cisco Meraki's AI assistant can surface insights and recommend next steps. But it only sees Meraki hardware, its advanced features are tier-gated, and it never actually executes a fix. Their own docs say to “validate its suggestions, especially for critical configurations.” Corax monitors your entire stack, across every vendor, and resolves issues autonomously before your team even knows there was a problem.
Licensing
Advanced features tier-gated per device
Flat monthly rate, unlimited devices
Visibility
Meraki hardware only
Every vendor, every platform, every protocol
Action
Suggests insights you still have to act on
Diagnoses, remediates, and verifies recovery autonomously
Scope
Network layer only
Network, cloud, applications, security, compliance, and tickets
Cross-platform
No visibility outside Cisco ecosystem
Correlates issues across AWS, Azure, Slack, ConnectWise, and 20+ integrations
Resolution time
Hours to days (manual intervention required)
Under 3 minutes average (fully autonomous)
Corax AI SIEM + OffSec
Awareness. Alerting. Action.
Action-taking intelligence in a world of monitor-only solutions. Traditional SIEMs flood your screen with logs in jargon that requires an expensive engineer to decipher and act on. The ones that have added AI still wait for a human to prompt them before doing anything useful.
Corax AI SIEM + OffSec is different. Built with autonomous AI actions first, it sees events on your network, correlates them, finds root causes, triages, fixes, heals, and restores functionality. When intervention is required and no one is answering the call, five specialized AI agents deliberate independently and vote on the safest course of action, with policy veto power and full audit trails protecting your business from rogue instructions.
Awareness
Ingests logs from every switch, router, firewall, server, and endpoint. Builds baselines. Knows what normal looks like.
Alerting
Correlates events across systems in real time. Eliminates false positives. Escalates through SMS, email, and phone.
Action
Diagnoses root cause, opens tickets, executes fixes, and verifies recovery. No human prompt required.
Available as a virtual machine or physical rack-mount appliance. Your AI runs locally. Your data never leaves your network.
Integrates with your entire stack
Need support for equipment not listed here? Corax adds compatibility with any device, service, or cloud platform in minutes through AI powered research. Just submit a request and your team is ready to manage it.
Why Autonomous IT Works
AI sees patterns humans miss
Corax monitors all signals simultaneously, correlates events across systems, and learns per-environment baselines. A human can watch one dashboard. Corax watches everything at once.
AI acts in seconds
Detect, diagnose, and deploy a fix in under 3 minutes. No waiting for someone to wake up, log in, read the alert, and start troubleshooting. The fix lands before the coffee brews.
AI never forgets
Institutional knowledge persists across every shift, every hire, every departure. Corax applies the same rigor at 3 AM on a holiday as it does at 10 AM on a Tuesday.
The Corax Neural Engine was designed and validated by engineers with 60+ years of enterprise IT experience. The AI reasons at a senior engineer level because it was taught by senior engineers.
21,502 infrastructure scenarios and counting. 100.0% detected and diagnosed correctly.
These are real scenario tests run against the Corax Neural Engine to verify detection, diagnosis, and remediation across every vendor, platform, and edge case. Fortinet, Meraki, Nutanix, AWS, Kubernetes, MPLS, SD-WAN, database failures, cascade outages, security breaches, and more. Every result is captured and public.
Scenario Results
Asterisk PBX Service Crashed — Calls Dropping
VoIP & Telephony / pbx_serviceThe Asterisk PBX service crashed due to a segfault in a channel driver. All active calls dropped and no new calls can be placed.
Kubernetes Secret Rotation Failure — Stale Credentials
Cloud & Container / k8s_secret_rotation_failureAn automated Kubernetes secret rotation job fails silently, leaving database credentials expired in 15 Kubernetes Secrets across 3 namespaces. Pods that restart or scale up pick up the expired credentials and cannot connect to databases. Running pods with cached credentials continue working until their connection pools recycle.
Java 21 (Spring Boot) DNS Resolution Failing — Cannot Resolve Dependencies on Windows 11 Enterprise
Server & OS / dns_failureJava 21 (Spring Boot) cannot resolve DNS names for its dependencies. All outbound connections failing with ENOTFOUND.
EC2 Instance Failed Health Check — StatusCheckFailed_System
Cloud & Container / aws_ec2An EC2 instance failed the system status check due to underlying hardware issues. Instance is unreachable. AWS recommends stop/start to migrate to healthy hardware.
RADIUS Authentication Server Down — Network Access Blocked
Network / radius_auth_server_downBoth RADIUS servers (backed by Active Directory) become unreachable after an AD domain controller crash. All 802.1X network authentication fails, preventing users from connecting to wired and wireless networks. Existing sessions remain active but no new authentications succeed.
Internal CA Certificate Chain Broken
Server & OS / internal_ca_chain_brokenThe internal enterprise CA intermediate certificate is revoked by mistake during a PKI cleanup. All certificates issued by the intermediate CA are now untrusted. Internal web apps, RADIUS 802.1X auth, and LDAPS all fail certificate validation.
PostgreSQL Connection Pool Exhausted — Idle Connections
Database / connection_poolThe PostgreSQL connection pool is completely consumed by idle connections from a misbehaving application that opens connections but never closes them.
OAuth2 Provider Outage — All SSO Logins Failing
Security / oauth2_provider_outage_ssoThe external OAuth2/OIDC identity provider (Okta) is experiencing a major outage. All SSO login attempts fail because the authorization endpoint is unreachable. Users cannot authenticate to any application that relies on Okta for SSO, affecting the entire organization.
Package Repository Corruption
Server & OS / package_repository_corruptionThe internal package repository mirror becomes corrupted after a failed rsync, causing all package installation and update operations across the Linux fleet to fail. Servers cannot install security patches or new application dependencies.
Kaseya VSA Agent Heartbeat Loss
Infrastructure / kaseya_vsa_agent_heartbeat_lossThe Kaseya VSA server loses heartbeat connectivity from 150 managed endpoints simultaneously after a VSA server renewal breaks the agent communication channel.
WatchGuard Firebox BOVPN Tunnel Flap
Network / watchguard_firebox_vpn_tunnel_flapA WatchGuard Firebox M590 experiences persistent BOVPN instability to 6 branch offices due to a phase 2 SA lifetime mismatch after a firmware upgrade, causing intermittent branch connectivity.
WebSocket Connection Storm — Server Connection Limit Reached
Infrastructure / websocket_connection_stormA mobile app update with a WebSocket reconnection bug is causing millions of simultaneous WebSocket connection attempts. Each failed connection immediately retries, creating a connection storm that exhausts the server's file descriptor limit and blocks all new connections including the web application.
Every test runs against the production Corax Neural Engine with full AI-powered root cause analysis. Issues Corax can fix autonomously are auto-healed. Everything else triggers remote hands dispatch via phone, email, or API.
Watch Corax Think
Every anomaly goes through detection, deliberation, and safety checks before action. No black boxes. No blind automation.
Teams that scaled without hiring
Early adopters on what Corax delivers
“We manage 40 client networks with a team of three. Before Corax, that would have required at least 10 engineers. It handles the overnight monitoring, the security scanning, the compliance reports. We just focus on relationships and growth.”
“Our funnels run through GoHighLevel, three ad platforms, and a custom checkout. When something breaks at 2 AM, leads just vanish. Corax watches all of it and auto-heals the integration failures before we even lose a conversion.”
“I was skeptical about autonomous remediation. But the approval gates and audit trail gave us confidence. Corax caught a certificate expiration across 12 servers that our previous monitoring completely missed.”
Meet Your IT Department
14 AI specialists, each an expert in their domain. They work together around the clock so your infrastructure runs itself.

Oracle
Nathan Cross
Neural AI
“I think, I reason, I decide.”

Amplify
Megan Cole
Marketing
“I watch your funnels, ads, and conversions around the clock.”
Sentinel
Sam Weston
Monitoring
“I never sleep. I watch everything.”

Chronicle
Ben Archer
Reports
“I turn data into stories clients understand.”

Ledger
Laura Briggs
Cost Ops
“I find the waste and forecast the future.”
Scribe
David Kim
Auto Docs
“I document everything so your team never has to.”
Atlas
Marcus Grant
Topology
“I map every wire, every hop, every path.”
Command
Tom Gallagher
MSP Ops
“I manage your clients so you can grow.”

Dispatch
Ryan Mercer
Tickets
“Every request tracked. Every SLA honored.”
Ranger
Jake Torres
Agents
“I deploy and command every agent in the field.”
Compass
Scott Palmer
Intel
“I see the patterns that drive business forward.”

Auditor
Priya Ashford
Compliance
“I keep you compliant so you can sleep at night.”

Bridge
Anika Sullivan
PSA Sync
“I keep your PSA and Corax in perfect sync.”
Garrison
Jack Harmon
Security
“I detect threats before they become breaches.”
Enterprise IT operations. Mid-market pricing.
The IT department you'd build if you could afford one. Every plan replaces six-figure engineers and five-figure tool stacks at a fraction of the cost.
Start any plan today. If Corax doesn't earn its keep within 14 days, email us for a full refund. No questions asked.
See PlansCore
For growing teams (25–75 employees) ready to replace reactive IT with autonomous operations
Replaces a $95K/yr sysadmin + $15K tool stack
- Monitoring (HTTP, DNS, SSL, PING, TCP, SNMP)
- AI diagnosis and autonomous healing
- Ticket management and full audit trail
- Network discovery and topology mapping
- 500 AI actions/mo included
- Email, SMS, and voice alerts
- Weekly operations reports
14-day money-back guarantee
Professional
Complete autonomous IT operations for multi-site teams (75–150 employees)
Replaces a $155K/yr engineer + $40K tool stack
- Everything in Core
- Full autonomous healing and remediation
- Agent deployment across all locations
- Security scanning and SIEM appliance
- Compliance automation (HIPAA, SOC 2, PCI)
- Voice escalation (RealSpeak AI)
- 2,000 AI actions/mo included
- Monthly reports + quarterly business reviews
14-day money-back guarantee
Business
Full IT department capabilities for complex environments (150–500 employees)
Replaces a 3-person IT team ($350K+) and 8–12 vendor tools
- Everything in Professional
- Offensive security testing (VANGUARD)
- Custom workflow automation (ReWire)
- Auto-documentation (Scribe)
- Business intelligence (Compass)
- 5,000 AI actions/mo included
- Dedicated success manager
- 2-hour priority SLA
14-day money-back guarantee
MSP Partner
White-label Corax for your managed clients. Deliver autonomous IT at scale.
Your clients pay $100K–$150K/yr for MSPs. Deliver more for $18K/yr.
The math for MSPs
10 clients × $1,499/mo = $179,880/yr in platform costs. Your clients get 24/7 AI-powered coverage. You keep the margin.
Enterprise
500+ employees or regulated industry? We offer dedicated infrastructure, custom compliance frameworks, and white-glove onboarding.
All plans include monitoring, alerting, ticket management, and AI diagnosis at no extra charge. Usage-based charges apply only for AI actions beyond your included allotment ($0.10/action), SMS ($0.01/msg), voice escalation ($0.10/min), and report generation ($0.15/report).
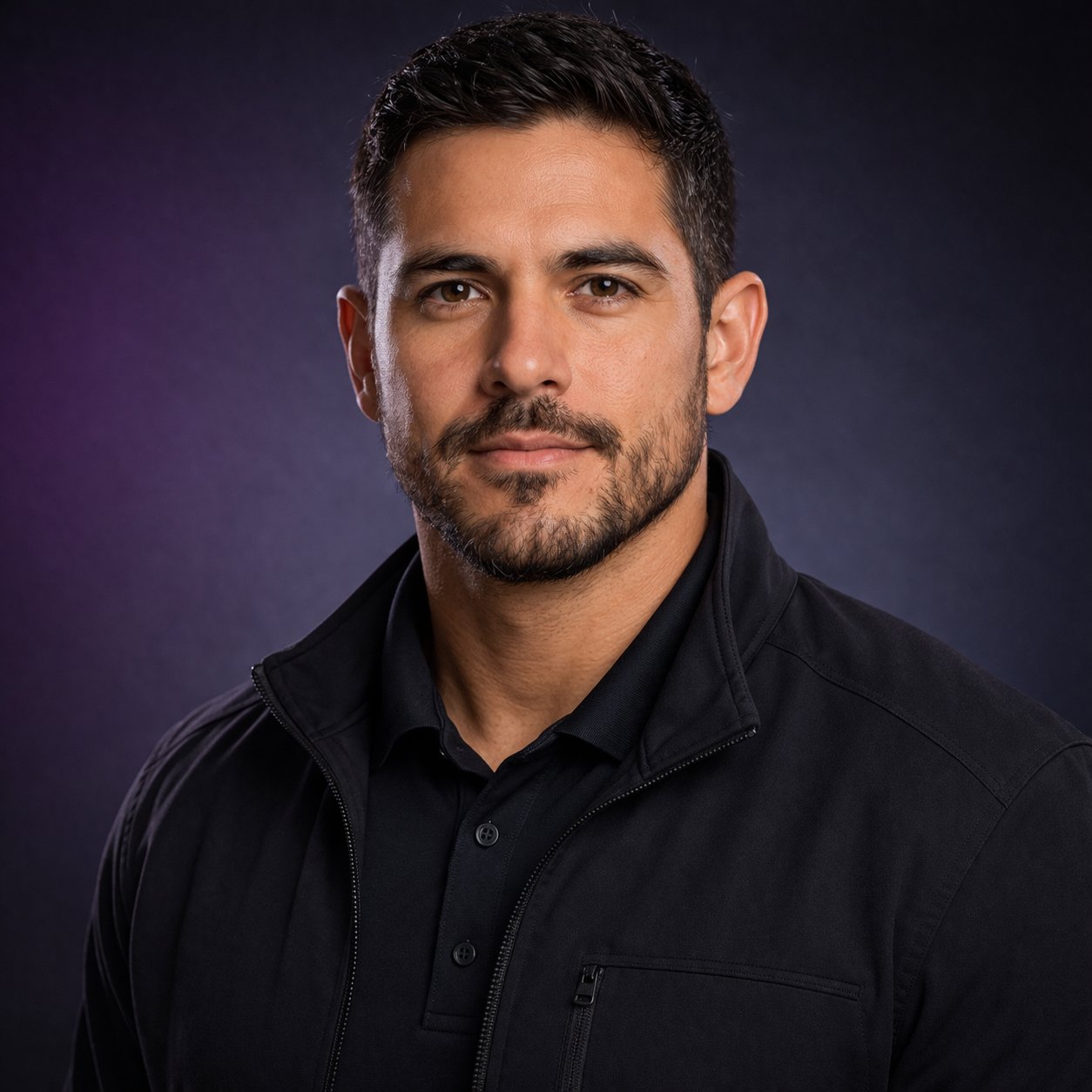
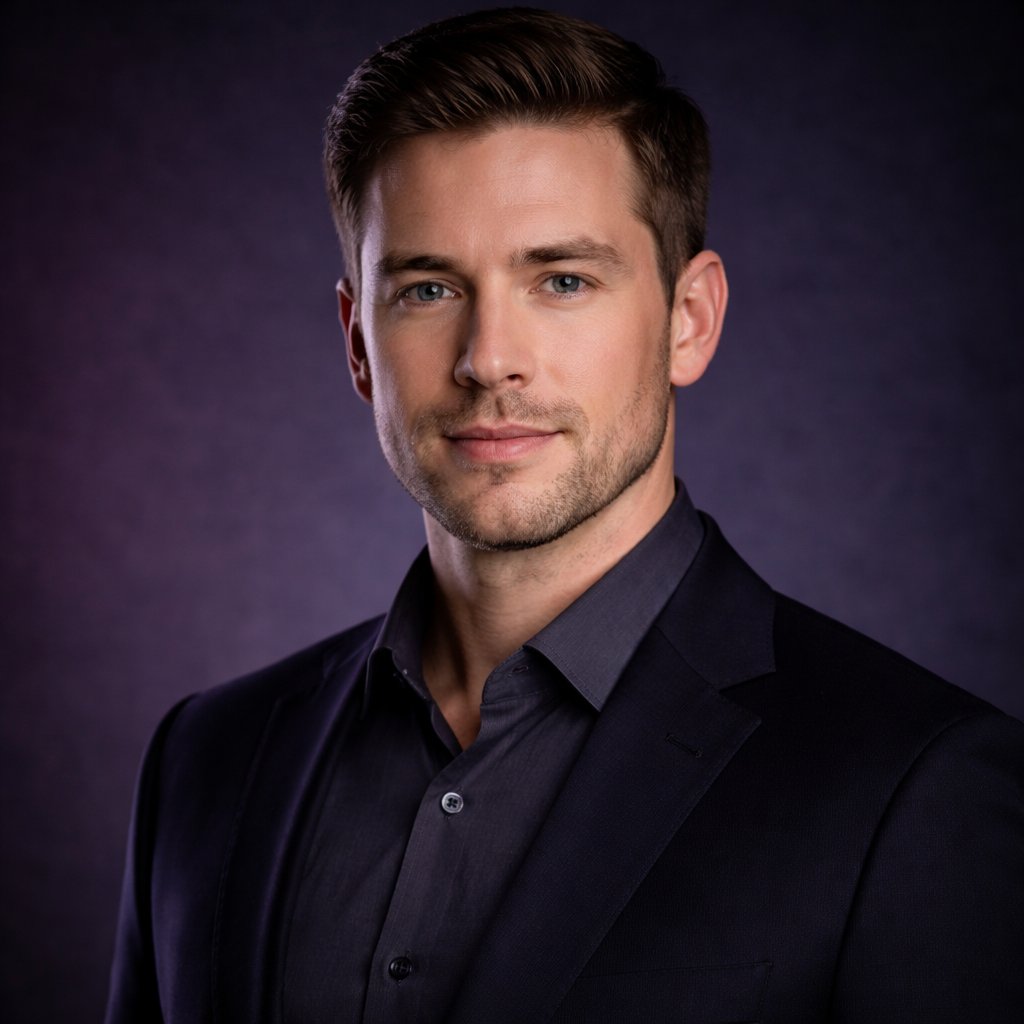
Built by Engineers with Enterprise Class Experience
Corax was founded by senior infrastructure engineers with over 60 years of combined experience managing enterprise networks, data centers, and cloud environments at scale.

Co-Founder & Principal
Senior infrastructure engineer with over 30 years of expertise across enterprise networking, systems architecture, and cloud operations. Previously Systems Engineer III at GreenPages Technology Solutions (now Blue Mantis), where he designed and managed complex multi-tenant environments for enterprise clients. Before that, Senior Network Engineer at Anvil International, owning the full network stack across manufacturing facilities. Ed built Corax to solve the problem he saw firsthand: businesses forced to choose between understaffed IT teams and expensive managed service contracts, with neither delivering truly proactive coverage.

Co-Founder
Cloud Identity Architect and systems veteran with over 30 years designing, securing, and modernizing enterprise infrastructure. Previously Data Center Manager for Microsoft's Technology Center, where he directed a 40-rack facility and led a cloud transformation initiative that halved the physical footprint through Azure migration. Led enterprise change governance for large-scale federal infrastructure at Salient CRGT, improving change success rates from 10% to 98%. Today he architects hybrid Microsoft 365 and Entra ID environments, implements Conditional Access strategies, and automates operations with PowerShell. CompTIA Security+ certified.
Scale your coverage. Not your payroll.
Pick a plan, deploy Corax, and give your team the coverage of a department ten times its size. 14-day money-back guarantee on every plan.